8 Best Anti Ransomware Tools You Must Be Using In 2017
In the recent past, ransomware has emerged as
one of the most challenging cyber security threats. This has demanded
the need for anti ransomware tools that one needs to use. Some of the
notable tools like Bitdefender, Malwarebytes, Kaspersky, etc. use
advanced methods to take preventive measures and block such attacks.
Many ransomware removal and decryptor tools are also available for
getting back your files.
Over the course of past year, we kept telling you about different ransomware attacks, including the likes of
Locky,
Cerber,
Jigsaw,
KeRanger,
etc. Many security experts also called ransomware the biggest threat we
would see in upcoming months. This prediction came true with the
arrival of
WannaCry ransomware.
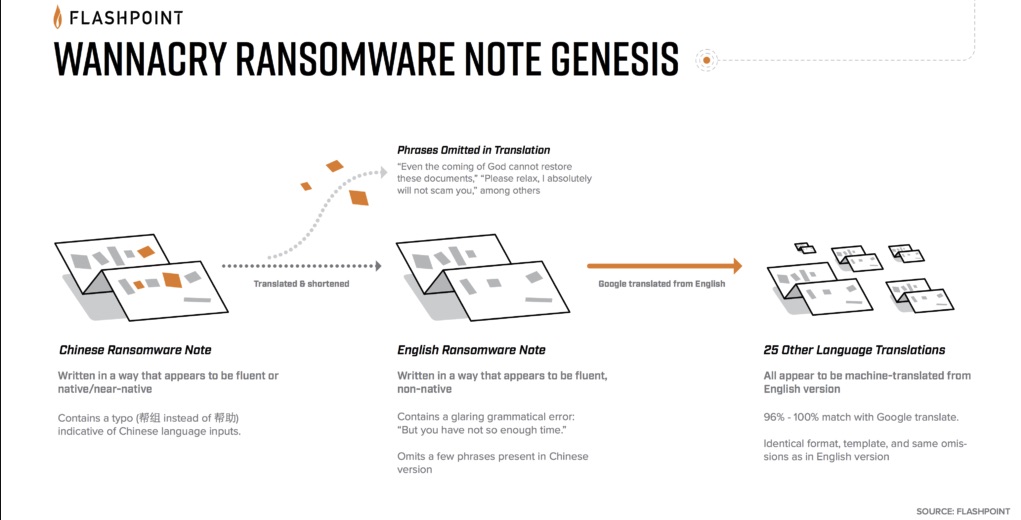
WannaCry ransomware, which used 2 NSA hacking tools leaked by
ShadowBrokers, was able to infect hundreds of thousands of computers
running unpatched Windows systems. It has been predicted that such
threats are only going to increase in upcoming months. So, apart from
following the
basic internet security practices,
what should you do? If you wish to save you Windows PC from threats
like ransomware in future, it would be a good idea to take a look at our
list of the best anti ransomware tools for 2017:
Top anti-ransomware tools in 2017
In our article of
top antivirus software of 2017,
Bitdefender topped the list. The multidevice license of Bitdefender
lets you select the preferred platform and enjoy advanced features like
malicious URL blocking, on-demand scan, etc. But, what about ransomware
protection?
Talking about Bitdefender Antivirus Plus, it’s a complete suite that
kills most types of Trojans, ransomware, and malware. Its ransomware
protection in Bitdefender allows you to choose folders that one wants to
be protected. This anti ransomware tool of Bitdefender comes with a
flexible configuration as compared to other solutions. You can also use
Bitdefender’s free anti ransomware tool that runs silently in the background provides protection against ransomware like WannaCry, Locky, TeslaCrypt, Petya, etc.
In the recent times, while talking about best anti ransomware tools
and anti-malware solutions, Malwarebytes appears towards the top of the
lists. Due to the sophisticated nature of ransomware, many basic
security software fail to prevent you. To save yourself from such
threats, you need solutions like Malwarebytes.
Malwarebytes 3,
which promises to deliver all-round protection like Bitdefender, comes
with a great anti ransomware tool that protects your files. Apart from
ransomware threats, Malwarebytes also protects you from fake websites
and links. It wraps the programs and browser into 4 defense layers and
stops attacks that exploit different vulnerabilities. Last year, the
company also launched Malwarebytes Anti-ransomware Beta.
The reputed cyber security firm Kaspersky offers a dedicated tool to
numb the ransomware infections. Created for keeping businesses and small
organizations safe from ransomware, this tool is available as a free
download. Just like most of the security suites, you don’t need
Kaspersky Lab security suite to be installed on your computer. You can
download this great anti ransomware software by visiting this link and
add an extra layer of protection.
Just like Bitdefender and Malwarebytes, the primary product of the
company, Kaspersky Internet Security, comes loaded with anti-ransomware
functionality. It also tells you about notorious websites and links to
make your internet browsing experience even better.
Trend Micro Security is another antivirus suite that comes with a
great anti ransomware tool that minimizes the risk of infection. The
latest release of Trend Micro antivirus comes with a strong focus on
ransomware removal software and protects you from WannaCry ransomware.
It comes with a Folder Field feature that adds an extra defense layer
to files inside a protected folder. It prevents notorious ransomware
from encrypting your files. The Folder Field feature prevents every
process or service from accessing the file inside that particular
folder. The company also ships Ransomware Screen Unlocker tool for
ransomware removal from infected PCs.
Ransomware malware are known for holding your important files in
ransom and demanding money in return for access. So, one must use a
reputed software to recognize, remove, and prevent ransomware.
Consistently rated excellent by experts, Avast 2017 deals with prevalent
threats like ransomware in an efficient manner.
In Avast 2017, the company integrated AVG’s behavior analysis
technology named Behaviour Shield. It sniffs the software for suspicious
behavior and exposes the sample of ransomware by analyzing the code
behavior. The company claims that Avast Behaviour Shield is capable of
stopping new ransomware variants, which makes it one of the top
anti-ransomware software around. Avast also provides multiple ransomware
decryptors for removing ransomware and decrypting your files.
Based in Turkey, Zemana specializes in security for business and home
users. They claim to make security programs with an easy-to-use
interface for general users. After the initial launch of Zemana
AntiLogger, the company launched Zemana AntiMalware which was designed
to scan and clear a computer from malware. It also provides real-time
protection and browser cleanup functions.
Zemana Antimalware is based on its own signature database that
removes the known and yet-to-be-born malware threats. One of the plus
points of Zemana Antimalware is its lightweight and highly optimized
nature that stores the virus definitions in the cloud to avoid
cluttering the PC. In many independent security tests, including MRG
Effitas, Zemana Antimalware was judged the best anti ransomware tool
that one can use. It’s available in two versions. While the one with
limited features is free, the commercialized version comes with a 14-day
free trial.
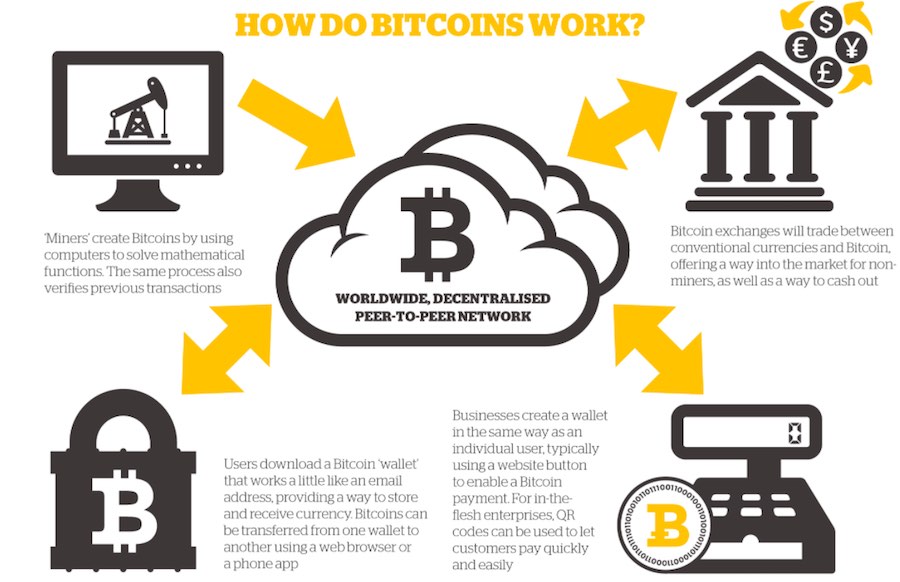
In the times like these where ransomware threats like WannaCry lock
down people’s computers and demand ransomware, the need for an efficient
anti ransomware software isn’t disputed. McAfee is a renowned name in
the realm of cybersecurity. So, it would make sense for a McAfee product
to make an appearance on this list of the best anti ransomware tools.
Here, I’m going to tell you about McAfee Ransomware Interceptor
(MRI). It’s an early detection tool that prevents the file encryption
attempts made by a malware. By utilizing, machine learning and
heuristics, this anti ransomware tool monitors and terminates the
processes that resemble the characteristics of ransomware. Currently,
this product is available for Windows 7 and later.
8. Tools to remove ransomware and decrypt files
In the points mentioned ahead, I’ll list some of the popular means to
remove ransomware from your computer and decrypt files. These
ransomware removal tools are useful when your computer is infected with
ransomware and you need to get rid of them —
- Nomoreransom.org website is backed by top security and tech giants. Here, you can upload encrypted files and find a free decrypting solution.
- Noransom.kaspersky.com is another online source that provides ransomware decryptor and removal tools.
- Avast, Trend Micro, AVG, and McAfee too provide tools to get rid of ransomware.