WannaCry Ransomware Hackers Are Most Likely From China
Since the arrival of WannaCry ransomware, the researchers have been unable to find the exact forces behind the attack. A new analysis by Flashpoint highlights the possibility of WannaCry’s affiliation to Chinese hackers. The firm performed a linguistic analysis of ransom notes in WannaCry samples and arrived at this conclusion. There are some things we know about WannaCry ransomware for sure. It was created by cyber criminals using an exploit that was the part of NSA’s exploit leaked by a group named The Shadow Brokers. The ransomware went on to affect hundreds of thousands of computers running Windows 7, Vista, and XP.
It’s possible that we may never know about the exact creators of this ransomware who locked the PCs of innocent users and demanded ransom. But, a recent research from the security firm Flashpoint points a finger towards a Chinese connection.
In a blog post, Flashpoint has listed the results of its linguistic analysis of WannaCry ransomware messages. The team analyzed the ransom notes individually for content, accuracy, and style.
Flashpoint found that WannaCry samples had language configuration files with translated message in different languages. It was found that almost all notes were translated using Google Translate. Only one English and two Chinese notes were likely to have been written by a human. It was also found that the English note was used as the source text for other translation and its writer could’ve been non-native.
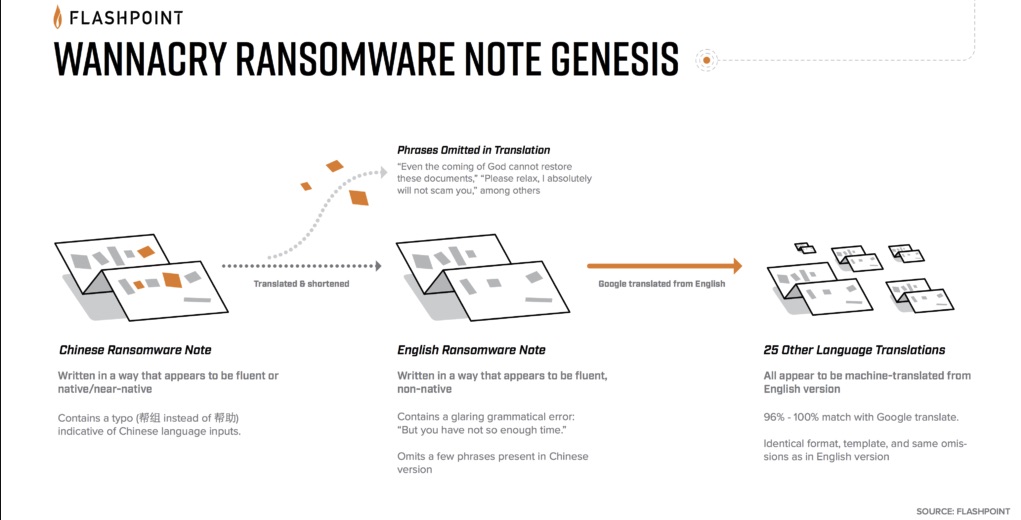
Coming back to the two Chinese notes, they were different from each other in format, content, and tone. Google Translate also fails in Chinese-English and English-Chinese conversion tests.
The analysis revealed certain unique characteristics that indicate that a Chinese expert wrote it. A specific typo made it clear that the note was written using a Chinese-input system. The Chinese note also used proper grammar, punctuation, and syntax.
The text has certain terms that narrow things down to Southern China. A compelling indicator was the lengthiness of the Chinese note.
While Flashpoint underlines the possibility of a China-based force, they don’t forget to mention that such hints were intentionally included to mislead. You can read about the research in detail here.
No comments:
Post a Comment